OSCP 2023 - How I passed in 30 days
The journey from noob to slightly smarter noob

In this article I want to share my OSCP journey and talk about how I was able to achieve a passing score on my 2nd OSCP attempt in May of 2023. I will briefly touch on my professional background in Offensive Security and share tips and advice that I picked up during my preparation process. To anyone studying for this exam I hope you find this beneficial in your studies and good luck!
Background
So before we get into this - I feel that it's important to touch on my background to set the scene for where in the imaginary penetration testing "skill ladder" I was when I took my exam. Not everyone starts from the same place.
The Beginning
Upon entering the Cybersecurity industry in August of 2021 I knew next to nothing about 'pentesting'. I was very very new to everything, including even just using a terminal for basic tasks. After about 7-8 months of learning on the job and an announcement from Offsec stating Active Directory would now hold a huge role in the exam, I sat down for my first OSCP attempt in April of 2022 feeling naively confident.
I will spare you the details but in short, my first exam attempt was a total wash - I was utterly unprepared in almost every aspect and struggled beyond belief with simple things - like file transferring and even getting reverse shells for example. I had only completed 4 boxes in the old-style OSCP labs. Since I spent so much time reading the course PDF and didn't get as much practice as I wanted to, I really can't count my first attempt as a 'real' attempt. Needless to say no passing score was achieved that day. however, it was at that moment that I knew one day I would be back, and this time there would be no chance of failure.

So fast forward to when I sat down for my 2nd OSCP attempt. I was no longer brand new to pentesting at this point, and I was lucky enough to already work as a penetration tester in my day job. I know most students or folks aiming for this exam won't have the luxury of the 'accelerated' learning environment I was in, so it should be noted that working as a penetration tester obviously helped me in my preparation for the OSCP. Despite this, I still spent a considerable amount of effort in preparing for my second attempt.
At this point I had almost 2 years of real penetration testing experience spanning everything from your typical external penetration test to performing physical penetration tests. It was also at this point that I had confidently conducted numerous Internal/Active Directory penetration tests and felt roughly comfortable when compromising a typical enterprise network environment. Furthermore I had completed numerous modules on TryHackMe including the Jr. Penetration Tester Path and the Offensive Pentesting path as well as passed both the PNPT and Sec+. This being said
I was comfortable in a terminal
I had a good idea of the key things one would do when trying to compromise both a single machine and network
I had a general idea of the flow and progression when completing a "Box"
I had spent enough time struggling that I now understood how I needed to study in order to fully prepare for the exam
I understood what information was important in a penetration testing report and how to explain an attack chain
With the stage set about where I was when I took my second attempt, lets talk about how I confidently passed after 30 days of focused preparation.
Preparation
So 30 days..how did we do it? Well background experience aside, it came down to 30 days of intensely focused studying. What do I mean by this? Well
The very day I obtained access to the PWK-2023 course I scheduled my exam for 30 days away and that very night I was working on the first challenge lab
My days (where allowed) and evenings were spent studying
My weekend's were largely spent studying
When I started the course I set myself on a path and told myself it was going to be done. Simple as that. I remained disciplined and focused throughout the whole time. I was going to study for 30 days and we were going to pass and that was final.
From a high level I broke down the big scary evil "OSCP Exam" into the core pieces and compartmentalized my learning into specific skills I needed to work on. I was already largely confident in my AD skills so I focused on things like
Initial access - Understanding what ports/services could be used for access and how to enumerate them
Privilege escalation - what tools do I use once I actually get a shell
- What are the main "collection" of priv-esc vectors I need to be familiar with and how do I exploit them
Post-Exploitation - Once I had administrative privileges what things should I be looking for and what tools do I run at this point
Prior to obtaining the actual course material I had been casually working thru various platforms seen below:
TryHackMe
Jr. Pentester Path
Offensive Pentesting Path
Wreath - DO THIS ROOM
Linux/Windows Priv-Esc Arenas
Proving Grounds
- I focused on the TJ Null List found here
TCM Security
PEH Course
External Pen-Test Playbook
Linux/Windows Priv Esc Courses
If there is one module you do from this list it should be the Wreath room on TryHackMe. Wreath is a fantastic room that will teach you the basics of network pivoting with various tools - a key technique you must be familiar with for the OSCP exam.
I also want to note that you don't need to have done all of these modules/courses in order to be prepped for the exam. These were just resources I worked on in-between my 1st and 2nd OSCP attempt.
The Course
The new and improved OSCP/PWK-2023 course brought a good mix up upgrades to the course material and the labs provided to students. You can read more about specific changes made here.
Given my background and previous knowledge of the PDF/exercises I was able to gloss over most of the content in the PDF except for a few key chapters. I will say the content in the privilege escalation chapters was great and really beneficial when working on the labs and on the exam.
Overall, I think the changes made to the course and content were beneficial and if you are lacking in a certain skill in your exam prep the course PDF serves as a great root of learning.
The Labs
If there's one thing you read in this article...it's DO THE LABS.
I strongly believe the labs are now the BEST resource you can use in your preparation. With the addition of 3 practice exams you now have the ability to take a real practice exam that mimics not only the difficulty of the actual exam but the format of the exam as well (3 standalones + 1 AD set).
The new and improved "challenge labs" were fantastic practice and really made up the bulk of my prep. The addition of an isolated lab environment which allowed the student to freely practice without the worry of suddenly losing connection because another student decided to revert a machine was a long overdue and welcome upgrade.
I felt that the labs were straightforward but reasonably challenging. The labs allow you to get plenty of repetitions and practice with important skills you need to know in order to pass but doesn't force you to endure an endless cycle of banging your head on a keyboard.
Key skills you'll run thru in the labs are:
Typical port scanning and enumeration
Practice with obtaining initial access and stabilizing your initial shells
Enumerating privilege escalation vectors and exploiting them
The concept of post-exploitation looting. Getting admin is great but what do you do once you are an admin?
File transferring - you should be completely familiar with general file transferring by the end of the labs
Pivoting Pivoting Pivoting
Of particular importance for success on the exam is the concept of pivoting and being able to leverage a compromised machine to obtain access to a new network of machines via your access as an attacker. If you are already familiar with pivoting via the classic proxychains + chisel method, I highly suggest you give Ligolo-NG a shot. You can read more about using Ligolo-NG here.
Luckily for you I've also created a simple video demonstration on how to use Ligolo-NG specifically for the folks who might want to use it in the PWK labs. You can watch it here:
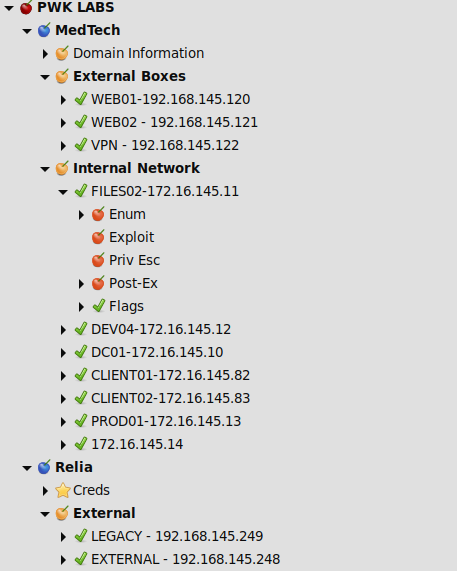
Another Important thing to note is that I placed a considerable amount of effort on my note-taking and organization. While I am a normal Obsidian user, I found that cherry-tree was just better as a "live" note taking platform as I worked thru the labs. Below is a snippet of how I setup my cherry-tree notes during the labs.
Overall, if you are a student taking the course now I would recommend you primarily focus on completing the labs and getting in those reps. Repetitions will build muscle memory and strengthen your methodology.
Throughout my time in the labs I had to use various tools for Privilege Escalation. One tip I'll emphasize is build a folder dedicated to storing all of the priv-esc tools you use and encounter in your prep. Below is the contents of both my Linux and Windows priv-esc tool folders. All of the tools below I used at one point or another in my preparation.
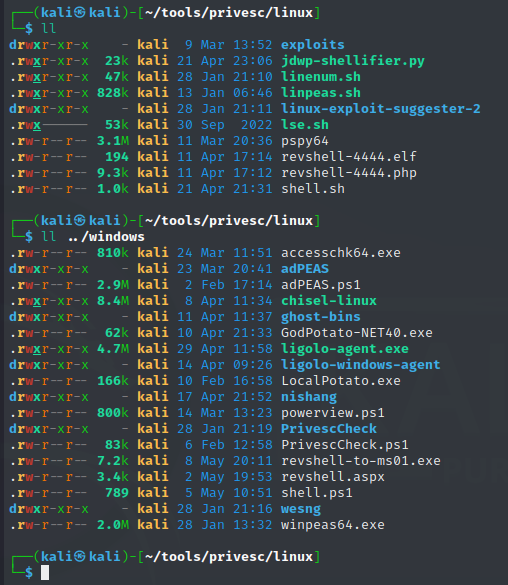
A couple I will highlight as my favorite are:
Linpeas & Winpeas
ADPeas - Useful for AD enumeration
PrivescCheck.ps1 - My go-to once I obtained initial access on a Windows target
Active Directory
Active Directory (AD) is a huge sphere of knowledge and there are just are so many attacks, tools and techniques to talk about that I couldn't possibly give them a proper overview here. I know a lot of folks are interested in the AD set so I'll briefly touch on AD skills necessary for success.
In AD, full compromise of a domain rests almost solely on one thing - initial access.
Initial access in the context of an AD pentest or and AD lab environment simply means that you have the credentials for a domain-joined user/computer account. In order to properly enumerate an AD domain and stage further attacks (kerberoasting) you need to have valid domain crededntials to do so.
Examples of valid domain creds can be having a user's username and clear-text password, or even having a user's username and their NT password hash for use in pass-the-hash attacks.
Some tools and techniques I recommend you learn and focus on practicing in the labs are
CrackMapExec - Your go-to all-in-one AD tool. Great for passing-the-hash.
Impacket - Impacket is not one tool but rather a collection of fantastic tools.
Impacket-secretsdump
Impacket-smb/ps/wmiexec
Impacket-mssql
Impacket-smbclient
Impacket-GetUsersSPNs
And many more
LDAP/SMB Enumeration
- LDAPDomainDump & CME are great tools for this
Kerberos Attacks
- Kerberoasting & ASREP Roasting
This isn't an exhaustive list of tools/techniques but you should definitely be familiar with the tools and attacks above.
Exam Day
The morning of my exam day arrived and I took a seat at my desk 30 minutes before my scheduled start time at 9AM. I hooked up to the proctoring software, turned on my camera and waved at the proctor with a smile. I was confident and ready to go.
With VPN access into the lab environment I kicked off AutoRecon scans on the 3 standalone boxes in the background and began on attacking the Active Directory set.
The AD set was conquered in 3 hours. Onto the standalones I went. After reviewing the output of my AutoRecon scans I went after a juicy target and in an hour flat rooted my first standalone.
I targeted the next standalone and obtained my first shell pretty quickly - I now had my 70 points. Even with 70 points I continued on. After a few hours and couple of unsuccessful priv-esc attempts I took about an hour dinner break.
After my 60 minute break I was refreshed and jumped right back into it. Shortly after I had rooted the 2nd standalone - 80 points! At this point I was feeling good - everything, all the exploits, shells and attacks had worked as intended! Everything worked just like it was documented in my notes!
For the next few hours I attempted to get initial access on the final standalone to no avail. Eventually I made the decision to review my documentation and begin on writing my report. I submitted my 80 point report shortly after midnight feeling relieved that the exam had finally been conquered.
Closing Thoughts
In conclusion, with proper discipline and time anyone can pass this exam. Everyone's path will be different and that's alright. All that matters is you focus on running your own race.
While I was able to spend 30 days in the labs and comfortably pass it's important to note that my journey to get to this level took roughly 1.5 years in total. It took many many long nights and quiet weekends to get to this point but with proper practice anyone can really do this - especially if I can.
If you've made it to the end of this article I hope you were able to get something out of reading my experience. Best of luck and feel free to reach out should you have any questions!